Cybersecurity Awareness Month 2020
The below newsletter was written by Mr. Richard Moormann of General Dynamics NASSCO – Norfolk for The Virginia Ship Repair Association Cybersecurity Awareness Month weekly e-mails! Please visit the VSRA Cybersecurity Committee page for additional information.
If You Connect It, Protect It!
It sounds so simple, but taking an active and conscious role in protecting your internet-connected devices is greatly important to staying cyber secure. Installing updates as soon as they become available, employing multi-factor authentication, deleting suspicious emails and attachments—following these simple every-day steps can vastly improve cybersecurity.
The first week of Cybersecurity Awareness Month highlights the ways in which internet-connected devices have impacted our lives and will empower all users to own their role in security by taking steps to reduce their risks. Commonly called the Internet of Things, or IoT, the risk to using the latest gadget that you can control from your smartphone could be greater than you thought. While commonly discussed in the household environment, the workplace is also fraught with problems. Let’s talk about a few examples.
When coffee makers are demanding a ransom, you know IoT is screwed!
Watch along as hacked machine grinds, beeps, and spews water! While this specific hack is a few years old, similar problems exist in products entering the marketplace every day. Just be sure you know what you are buying before you connect things up at the home or office. This example could cause a fire or other problems. Article at https://arstechnica.com/information-technology/2020/09/how-a-hacker-turned-a-250-coffee-maker-into-ransom-machine/

Some recommendations for home users of connected automation.
“…the proliferation of all these devices in our everyday lives also poses a security risk, as the gadgets and gizmos, unless secured properly, can be used as new avenues of attack by cybercriminals.”
https://www.welivesecurity.com/2020/10/05/5-steps-secure-connected-devices/
This site has an abundance of great information. This quote is apropos
Teach the Children Well
At home, we need to keep our kids in that loop too. That’s even more important now, with so many of us working at home and our kids doing school remotely. While the schools are still trying to figure out how to deliver classes at all, doing it securely is still a challenge. Though the fact that they are pulling it off is a tribute to our teachers. School aside, children are an easy target for Social Engineering schemes and a broad range of related attacks. When it was just Junior’s Chromebook, it was more of an annoyance than a serious threat. But now, that infected device may be the springboard an attacker uses to infect your work laptop, and from there, springboard into your organization’s work environment.
https://securityboulevard.com/2020/10/if-you-connect-it-protect-it/
Would you like to bring Alexa or Google Home to work?
Sounds amazing, just say “Alexa, email the most recent time cards to payroll.” or “Alexa, publish the revised schedule to the company portal.” Not so fast. For these nifty Smart voice assistants [SVAs] to work, they are connected to the net, processed by the home servers and then the data is retained for funny amounts of time. Why does it matter? A few reasons, like Trade Secrets, CUI, liability, and such. Never mind they are ALWAYS listening. Even when the ‘wake up word’ isn’t used, they are processing sounds all around them. In the future, the technology will likely be better segregated and more secure, but not today. Hot tip: you may want to disable those smartphone apps while at work.
This research article pulls some other interesting results.
https://truedigitalsecurity.com/blog/smart-office-devices-come-with-security-risks
“Smart voice assistants are very susceptible to exploitation by malware and threat actors and can be used to facilitate or fall victim to botnets, DDoS attacks, espionage, and social engineering campaigns”
IoT in the industrial workplace?
Called “Industrial IoT” [IIoT], it means more connections and automation in industrial environments. Plasma cutters, HVAC, fire prevention monitoring, water pumps, assembly lines and more, once serially connected Supervisory control and data acquisition [SCADA] devices now have Ethernet or WiFi connections for additional functionality. The world will never be the same. Thanks to IIoT, the machines will be able to talk to each other to take over the world! But also, since they are interconnected, there are more security risks. Some organizations fail to isolate the IIoT devices from administrative networks. This is a bad practice, not helped by manufacturers of such devices who build for user convenience, vs security. Bad actors have another vector to access the workplace. Most any connection can be exploited, if not properly locked down and monitored. Mitigations can usually be made, but there could be additional costs, or purchasing additional features and maintenance subscriptions may solve many problems. Before purchasing systems with such features, ask your computer security team to conduct a document review, proof of concept testing, and risk assessment.
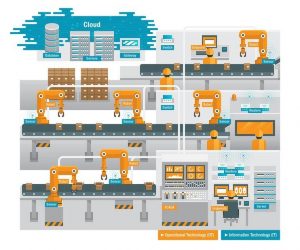
ioot smart factory
Image Source: TrendMicro
Here are other articles for deeper reading:
https://www.datashieldprotect.com/blog/what-is-scada-iot
https://www.trendmicro.com/vinfo/us/security/news/internet-of-things/-the-iiot-attack-surface-threats-and-security-solutions
White papers: [very, very deep]
https://core.ac.uk/reader/160031710
https://documents.trendmicro.com/assets/white_papers/wp-identified-and-authorized-sneaking-past-edge-based-access-control-devices.pdf
Learn more at this Upcoming Webinar:
Smart Devices Need Smart Security: Securing Your Business in an Internet of Everything World
October 13, 2020, 2pm Eastern, 11am Pacific
To recognize Cybersecurity Awareness Month, NCSA and partners will come together on October 13th to discuss smart device security for small & medium-sized businesses.
- As you purchase more of these smart devices/internet of things devices (IoT) and bring them into your home and business, what are the security risks?
- What steps can you take to minimize those risks?
- What are policy considerations for employees using smart devices?
We’ll discuss all this and more. Bring your questions. We’ll save plenty of time at the end for Q&A.
https://staysafeonline.org/event/smart-devices/

